37C3 - Finding Vulnerabilities in Internet-Connected Devices
HTML-код
- Опубликовано: 7 янв 2024
- media.ccc.de/v/37c3-11919-fin...
A Beginner’s Guide
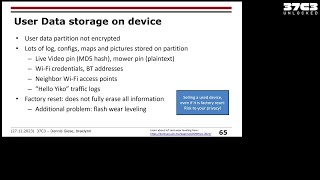
This introductory session will outline the process of hacking internet-connected devices, with the help of a real world example: Poly telephones and conference speaker systems. We will explain vulnerabilities we identified in them and how they can be leveraged to transform the devices into wiretaps.
In this introductory session we will journey into the field of internet-connected device security. Our talk aims to empower beginners by simplifying the process of hacking such devices.
We'll discuss vulnerabilities we uncovered in Poly telephones and conference speaker systems and describe how we effectively transformed a seemingly innocuous conference speaker into a fully functional wiretap. We'll begin with straightforward findings accessible to beginners and progress to more technical discoveries, so that people with no experience in the field can follow along, too.
By the end of the talk, the attendees will have a foundational understanding of how they can approach hacking such a device and will have learned how the impact of vulnerabilities can be shown and increased by chaining them.
All the vulnerabilities we discovered during our research have been responsibly disclosed to the vendor and will be published in December 2023.
Pascal Zenker
Christoph Wolff
events.ccc.de/congress/2023/h...
#37c3 #Security








Top Vortrag! Sehr informativ, vielen Dank 👍
super spannend - vielen dank!!! :)
Yep, that's the stuff! Good talk!
Very interesting talk, thanks a lot!
good talk to get into the whole subject!
fire talk!
Of course you ran Doom on it! Love it.
Nice work guys. Imagine what phun you could have if you could get your own custom firmware running on it.
Bbbf fschrieb. Die ebeee eeee😅😅b😅
Nice!
So fun.
21:53 😂 Made my day 😂
Ohh man, immer noch das alte Standard Admin Passwort (das war es schon beim ersten Polycom Telefon).
Ich war früher bei snom Produktmanager (viele viele Jahre ist es her), ich habe gegen das Murren einiger Kollegen durchgesetzt, dass das Telefon im Webinterface UND im Display vom Telefon anzeigt wenn das Admin Passwort NICHT gesetzt ist. Es gab zwar die Option die Warnung zu unterdrücken aber wer das macht ist halt selber schuld . . .
Sir!
22:18 "... they check for any unwanted characters..."
No! Bad Polycom! This is exactly the wrong way to "fix" this, quote the arguments instead.