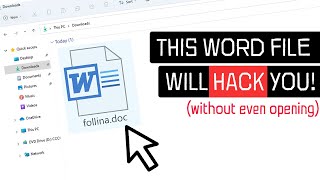
HACKERLOI.pdf
HTML-код
- Опубликовано: 16 окт 2024
- // Membership //
Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into exclusive ethical hacking videos by clicking this link: / @loiliangyang
// Courses //
Full Ethical Hacking Course: www.udemy.com/...
Full Web Ethical Hacking Course: www.udemy.com/...
Full Mobile Hacking Course: www.udemy.com/...
// Books //
Kali Linux Hacking: amzn.to/3IUXaJv
Linux Basics for Hackers: amzn.to/3EzRPV6
The Ultimate Kali Linux Book: amzn.to/3m7cutD
// Social Links //
Website: www.loiliangya...
Facebook: / loiliangyang
Instagram: / loiliangyang
LinkedIn: / loiliangyang
// Disclaimer //
Hacking without permission is illegal. This channel is strictly educational for learning about cyber-security in the areas of ethical hacking and penetration testing so that we can protect ourselves against the real hackers.








:)
:)
:D
I want to know that if it is possible to know is pdf okay or not without open it?
Ok sir then,how it'll work for Android
Missing the old intro 😥
Ay yes, now I can send my "Home work" to my teacher.
Yeah "home work"
Yeah "home work"
🤣🤣🤣
Ah yes, you just copied the same comment from Lio lang's malicous pdf video from 3 years ago and also doing this will get you expelled and arrested.
, 😂
This is really scary.. Thank you for spreading such amazing knowledge.
This very old hacking 🙂
But now hackers can do more scary things 🙂
@@rafimr5751 Ohh
@@rafimr5751 like what i really want to know just tell me the names
@@AmanKumar-hy5ck I can mine cryptocurrency on you device 😋
@@AmanKumar-hy5ck for that check my bio 🙂
i love the simplicity of your tutorials, keep going !
My favorite channel! Thank you Loi Liang Yang!
mr loi you are really genius,
love your content and ur way of simplifying the information
@Y K why not?
no
@Y K so just because he does a little easier tutorials, he's a script kiddy?
@Y K Yes, there is. but that's not really the point. You can't just claim that someone is something without knowing anything. Thats just hating ^^
@Y K 7, almost 8
There’s is few of questions I need to ask you which can a iPhone be used to do ethical hacking using ISH or etc? What about even a Chromebook tablet? Also how can someone get data from the air?
Also forgot to ask is it possible for someone with ADHD to become one of the best hackers? Currently struggling honestly even trying to make decent living but not giving up hope yet. Thanks I feel like your the best person to answer this honestly and one of my favorite teachers here on RUclips.
i love this channel, you make things easy
they ARE easy if he uses them on this channel
Mr. Loi you have amazing brain and amazing way to learn us how we do it, THANK YOU.
you can learn all he says from manual of the programs
@@sbypasser819 where is that manual?
when i set the playload how can i know the playload's file location?
and how can i know the email send to the target (demo)
If I use my Android Galaxy S9, rooted & with AFWall+ installed, will opening the pdf-file still be as malicious, as it was shown here?
You're not revealing some codes. Is there any course of yours? In which u have. Taught clearly everything? Because RUclips have restrictions I can understand that,
I have seen many people, teaching ethical hacking, but I want to learn from you , you're experienced, I want to connect with you please reply
I Would Definitely open this file.
In my organization's production server.
RIP✋️💀
Best in the game... Fav channel of all time... Much love 🔥🔥🔥
Loi we want tutorials about hacking android phones, because they are the most uesd phones in the space 😁.
Guys hit like to rise up my comment
he will not, he just showed you an outdated exploit, look at the video, he was using Adobe Reader 8.1 (Release Date: June 2007).
@@L2002 the fact that the viewer is outdated says literally nothing about the exploit itself
@@Daniel-yt7ry TYL3R DURD3N
Its only happen when the firewall and antivirus is disabled right? So keep your firewall and antivirus active and updated.
Well, a virus can add itself to exception and bypass those stuff so who knows. Never safe to completely just trust your anti-virus
@@Motoxrides a virus can not add itself an exception, the user needs to allow that exception xd..so...
@@danawhite7361 you haven ever seen viruses that did that? "The PC Security Channel" talked about such a virus a few years back.
@@TVPInterpolation need admin! user needs to agree
this video is so misleading. he's also using Adobe Reader 8.1, which means June 2007!!!! can you believe that?!
well.. 5:01 is the most important part. If you read WHAT you are opening there you will be just fine. Also, if you have the file in any other directory (in this case) you would not be trapped in a TCP reverse shell would you?
He's making real tutorials and all but he doesn't mention all that stuff on purpose, if you want to learn from him you are going to learn just the base (basically how to be a skid) and then you'll need to check yourself how to bypass all the other sh!t.
@@broz36_ i know bro. but many ppl here are conviced that there is nothing the target can do.
@@Suneeh1338 Yeah, he has to do something about it.
I mean, what can WE (the avarege viewer) can do about it?
It's not like you can make a YT channel and post the real sh!t there because it's gonna get taken down. (NullByte tried that)
Maybe making it into some puzzle so that only people that aren't just some "average viewers" can access and that will be outside of YT so it won't promote any illegal activities?
@@broz36_ exactly.
This exploit seems to be just for adobe reader, so you can just use firefox or microsoft edge (which is the default pdf reader on windows) to view the pdf
Sir, I don't know the path of the file "HACKERLOI.pdf" you created in the video.where is it....???
Me too i don't know where is the PDF file
I have the same question, someone know where is it?
@@felipearbelaez1360 just make a new document in the desktop and give it a name and embedd the payload inside that, thats it
Create black instead
set:payloads> Port to connect back on [443]: 1337
[!] Metasploit has not been previously run on the system. This means that the msf directories haven't been created yet. Running Metasploit for you.
[*] Waiting 10 seconds for the directories to be created...
[!] Please exit out of SET and type 'msfconsole' from the command prompt and launch SET again. Can't find the msf4 directory.
I use kalinethuner
How long does it take to payload generation to complete? It seems for me it takes a very long time or is just looping indefinently both with ubuntu and kali linux
I thought it was only mine, I've tried several times but it keeps generating with no results for minutes/hour
@@vincentcj7548 yes
Thanks you.
please I have a question
1. if the pdf file was opened on a smartphone it will be controllesd also?
Mr. Loi, i love this channel can you make a full explanation of how to use CVSS in every type of metric, thank you!.
I want to know without showing the permission pop up , taking access of CMD is possible or not? I know its possible but how
why you never use obfuscation, in the real world everybody has at least windows defender enabled.
and these payloads are easy to detect.
where pdf is stored?
I am a newbie. I read a document saying that to be able to insert malicious code into a file such as pdf, it will have a format like: abc.pdf.exe in your video. I don't see the exe extension at all. Was the documentation I read completely wrong?
yes, me too, i think it doesn't worok on gmail
Next time I'm sending out CVs for job applications, I'm going to use this XP
🤣🤣🤣
Can an internet security or an antivirus be able to stop this attack ? Say Kaspersky or Macafee ?
I love your videos but it would be nice to mention that you will have to first convince the victim to disable windows defender or do it yourself in any way :)
Is there a work around so that windows defender does not pick it up?
a normal payload can bypass windows defender but for pdf idk
Hi Loi, interssing but is a play for begginer create pdf malicious backdoor....you have explain what we can encode the PDF for AV. advanced tecnic for encoding...the shikata_ga_nai encode and other are old..and all AV detected. Explain some manual mode for encode PDF undetected sure.
I hope there will be a tutorial of how to detect if something happens to the user like this or a solution to avoid it like setting configuration or something. This makes me aware that not all doc/pdf files is safe. I wonder if this method is also applicable to videos. Like, when opening a video, it is also possible to get hacked.
I'm pretty sure that windows defender will block it
@@SunBlade4302 5:01 in the video.. he just accepts everything and OPENS it.. just read what you open guys :D
don't worry at all, this video is misleading. he was using Adobe Reader 8.1 (Release Date: June 2007). are you kidding me, 2007?
Yup even when opening an image
But its not that easy so not anyone can do it
And to be safe open unknown sources files on vps or rdp
Can you tell me how to do it with my own payload, I don’t want to have remote access just my exe to pass the Anti virus Softwares. (For ethical hacking only) We are tasked by our it school course in the realm of a project.
It doesn’t matter which exploit we use, the payload must do its job on target machine. The exploit adobe_pdf_embedded_exe doesn’t work since it’s for version 7.1 and we have version 21 at current times.
Amazing content . Thts all we can do in virtual environment. How can we get a meterpreter session for a device that is connected to public network i,e the internet.
is it detectable by windows defender or other antiviruses??
Amazing information. Love your videos. Regards from Sweden
Loi, won't Antivirus programs stop any pdf with an exe or some pdfs with exe attached the Antivirus programs will allow to pass if you crypt it properly with a never before seen crypter? Loi please answer.
there are encrypters for pdf files
@@pervysage4595 Can you tell me the name of one or more pdf encrypters? So what do they do? They will literally encrypt the pdf and the exe and make it look like what type of file to Antivirus programs?
@@mikevinitsky8506 you need to know basics of coding here, u can’t just use skid software abs expect to bypass av
@@edmorris4720 I'm a programmer. What is skid software?
@@mikevinitsky8506 lmao it means script kiddie. someone who uses other ppls stuff to hack and doesn’t write there own. like this backdoor maker. it won’t bypass av
Always motivated by your tutorials
When we sending a pdf document like in the video should we wait on the Kali Linux terminal ? Or we can close our laptop then re-open Kali *imagine* 2 hours after the victim open the doc and will it work?
this is just amazing than i expected, i love it
I have a create question. What would happen if you were to open it on any kind of phone?
Love you man, and thanks for yet another amazing video.
❤
Yeah but if the adobe program is cloosed wouldn't we loose reverse shell?
Handsome hacker indeed👀
Please tell how to stop accessing the pc, like how can i stop accessing my own pc. ik its weird question but at least tell me.
Old intro was dope. Bring it back please
excuse, but i don't understand where i can find the file HACKERLOI.pdf; after being renamed, in which directory is the file saved?
Can you tell where the file is stored so that I can send that pdf
bruh did you find out
i cant figure it out rip
Sir I'm trying this on AWS EC2 but i failed everytime, which ip should I use AWS public or private ip , i tried both but when I open pdf meterpreter not starting , i show started reverse TCP handler , not happening anything
What i do if i see you in my city
Run away
Just run don't look back
And hide your phone 😂
Everytime i get a payload is saves it to a root folder which i cant axcess any fixes?
Would love to hear a good tutorial on obfuscation, AV catches most of the stuff from SE
thats the where you need to learn to code comes in.
@@brodierobson4490 I'm guessing you work in education or a consultant or something. I agree that coding is important, but you can be in infosec with out being a strong coder. Obviously some python is important.
Hey, i am been hacked for. Long time. I have an doubt, may be he has sim jacking attack my sim because he had my all personal info, i am very worried. What should i do??
Thank you for your video. Can we have more details on the technical part ?
A pdf isn't supposed to be able to handle an .exe files.
How does the trick work ?
idk, but i think he's showing us an outdated exploit without any notes to gain views, if you look at the video carefully, he was using Adobe Reader 8.1 (Date: June 2007).??? 2007 Seriously???
@@L2002 this is for educational purposes only of course he wont teach stuff that you can exploit you should have common sense if you want to be a real hacker
@@OpenYoureyes304 i know that, but at least he should say if the exploit is outdated or now
I HAVE LINUX RUNNING IS A VM, WHERE DO I FIND THE PDF I CREATED??
Loi should be protected at all costs!
why? what he says can be learned from text sources
@@sbypasser819 not only that, he was using Adobe Reader 8.1 (Release Date: June 2007), 2007!!!
hey can anyone help ? ummmm i did what hackerloi did but it doesnt seems like is working , i put the path to a pdf file and after i done renaming it with setoolkit i copy that file and put it to window and it didnt work , is it because i dont have adobe reader on my windows ?
it already gets detected by windows defender ,,,, no use
yeah bro every msfvenom payload gets detected by antivirus gotta find the new way
@@renderset2937 True
@@renderset2937 you can make the metaspliote payload undetected by obfuscation
Do you know where the file is being saved after renaming it. I can't find it bro.
@@Rahul-nw5rp Google it
what do you think about starting a hacker group called
LoiSec
Thanks for teaching us real hacking ❤
thats ethical hacking
It's good to know this stuff but, any script kiddie can do this just as we are learning it or using it as a quick reminder/reference. To be a real hacker takes much more then using someone else tools.
@@SK-me9by to be real hacker you need to enable screen blocking and you need to know the keybinds for opening the system prompt function in hai.dll
I got this error : Sorry. This feature is not yet supported in Windows or Metasploit was not found.
Any ideas please??
You the best of the best .much love from South Africa
It's under your own wifi, or same machine you are using. How is about the machine out of your network???
i think we can do that using ngrok
Some question... if the victim computer has the port 4455 closed. This not work? Im tried this on my computers at home. The windows 10 computer has firewall and the windows defender is turned off. But anyway the os detected the file and removed it from usb. Thats a good thing of course but are you using a other version of windows or old version of adobe? Thx for informative channel!
infinite message "Waiting for payload generation to complete..." Could you fix that issue??
This might be a dumb question but I hope to get a reply from you or any expert
I'm new to all of this so my question is, are sessions permanent?
I mean will I lose the connection if I close my PC?
if so how can I keep it permanent?
It's not permanent, look up a tool called weevely.
But the pdf file is fishy since it prompts with some suspicious message before opening. How to avoid this?
Setoolkit says it's done creating/editing the PDF but there is still no PDF anywhere. Why is this?
5:01 well windows allready warns you about it, so read any pop up showed then click after reading carefully
This only works through adobe instead of using other pdf programs it will not work. right?
If a hacker did this would a factory reset remove the problem?
@DDD9216A oh true
How to use the same concept on IOS devices especially new updated iPhones, i've tried it many many times with different payloads but still not working
This exploit works only on Windows PCs?
What if I download a file like this and open it on phone with Google Drive PDF-viewer?
For those figuring out where the generated pdf is saved, the path is /root/.set
When im sending it it says “unable to connect to mail server” how did you send it? Can someone help please
yes u can't with gmail
does it work for computers on diffrent nets? like p2p or holw punchhing
When you click that your machine showing a warning message that it could be a virus. So how to make it then it undetectable?
Which kit or tool we have to use for make pdf payload for Android
Unable to connect to mail server. Try again (Internet issues?)
I am constantly encountering this error code. Can you help me?
Does this only work on one network on even if the person is using another network and opens the pdf file?
See the most recent member-only video on how to host listeners on the Internet: ruclips.net/video/sXQCE5Ed9Xs/видео.html
When I try this it says that "Unable to connect to the mail server. Try again (Internet issues?)" But there are not any internet issues at all. Sir, how can I fix this?
The main point is Even if the file has already been loaded onto the device, but not enabled that file Computers will still not have the risk of being controlled,am i correct?
how to find the path of the pdf we renamed please i didnt find it on desktop , thanks , and i appreaciate your work
After cloning the Social engineering toolkit, tried to install the requirement.txt but it is showing error like "ERROR: Could not build wheels for cryptography, which is required to install pyproject.toml-based projects"
Solution please
I would guess that this is not a persistent connection, right. Once the windows box is rebooted, the exploit dies unless pdf is opened again.
what is this tutorial for if the pdf is detected by all anti virus
HackerLoi you are my favorite Hacker to watch, you go through things quickly and precisely. Great job man.
Same
Please tell how to stop accessing the pc, like how can i stop accessing my own pc. ik its weird question but at least tell me.
@@zipp5022 If they already opened it that will do nothing.
@@addicted3105 You can go back to a previous version of your machine, assuming you're using windows.
What abt antivirus and windows defender scanning?
Do we need to disable them before running the downloaded file?
Can I get rid of the problem by delete it or move to trash bin?
I just had one question...if instead of firefox we write chrome will it still work....coz chrome is used by everyone
How will this work if you are working remotely? This only seems to be on a private Network.
What happens if you open a malicious Windows PDF on an Android device
What about AV/Defender Detection? Will that bypassed or not? Kindly reply Sir
windef picks it up
you need to know basics coding to obfuscate it, you can’t expect something like this to get past windows defender
Do you know where the PDF file saved?
In my metasploit it says started reverse tcp handler on my IP, and that’s all, I can’t find where to go to the file
I am wondering, if you also can not just start a reverse shell payload, but just execute a file, for example, when I dont have that much time to wait, until the "victim" opens the file, or if i dont need any reverse shell. Is that possible?
Hi Hacker Loi l, how can i get your full course on hacking ? Thanks!
what happens when that PDF open the file from an Android device ?
How do you think does Kali Linux has backdoors?
Does This Also Works on MAC? Apple Laptop/PC Devices?
What about windows defender and other antiviruses???? ....(asking for a classmate)
i realy like all your video i watch to all your video but how about samething new like pdf attack on android this will be really cool if you can do that and thankes you
its time to go to more advanced topics. I would like a video on how to create a botnet